TDE Fast Online Conversion transparently encrypts data at rest in Oracle Databases. It stops unauthorized attempts from the operating system to access database data stored in files, without impacting how applications access the data using SQL.
What is Oracle Transparent Data Encryption (TDE)?
- TDE enables organizations to encrypt sensitive application data on storage media, protecting the data at rest.
- TDE addresses encryption requirements associated with public and private privacy and security regulations such as PCI DSS.
- TDE cannot be used to obfuscate or mask the data for users who have privileges to access the encrypted tables.
- User with access to an encrypted table will be able to see the data in clear text because Oracle transparently decrypts the data for any user having the necessary privileges.
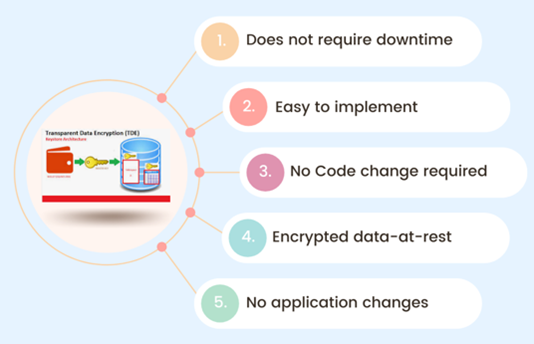
The Advantage of the Online Encryption Method
Before Oracle 12.2, it was not possible to encrypt OR decrypt a tablespace using simple commands, the only option was to use Data Pump to export or import data to encrypt or decrypt which requires downtime and a complex process.
The Benefits of Online TDE Conversion Include
Oracle Transparent Data Encryption Installation
- Oracle TDE is available by default in Oracle RDBMS Enterprise Edition.
- An Oracle Advanced Security license is required to use Oracle TDE.
- It requires no application code or database structure changes to implement.
- The only major change to database function is the Oracle Wallet which must be opened during database startup.
TDE Storage Overhead
Storage Overhead incurred by TDE column encryption is between 1 and 52 bytes for each encrypted value.
1) Algorithm used (AES-128, 192, and 256)
Adds one extra block of 16 bytes which depends on the (AES) algorithm used to encrypt the data.
2) Integrity check
20 bytes overhead for integrity check. This is OPTIONAL.
3) SALT
16 bytes overhead if ‘SALT’ is used to encrypt a column. This is OPTIONAL
Notes:
Only use “no salt” for EBS tables.
Tablespace encryption causes no storage overhead.
TDE Performance Overhead
The impact is limited to CPU performance.
- Data must be encrypted and decrypted.
- Highly dependent on access patterns to data Column Encryption.
- 5% to 20% CPU performance impact for several customers.
TDE Implementation Made Simple with Five Steps!
Step 1. Create a Wallet/Keystore location.
Step 2. Create the entry to the parameter file.
Step 3. Set the TDE_CONFIGURATION dynamic initialization parameter.
Step 4. Connect the system to the root container and create the Keystore.
Step 5. Create the Auto-Login Keystores.
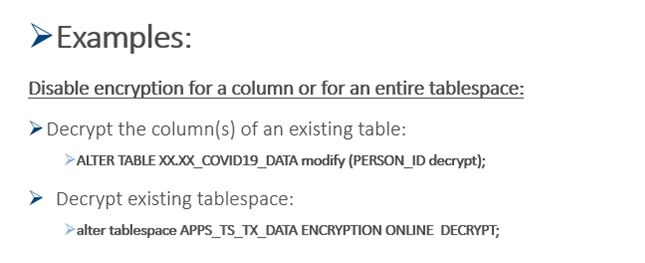
Is It Possible to Remove or Disable TDE?
 It is not possible to remove TDE once implemented. Even if there are no encrypted objects in the database, the TDE wallet has to be present in the wallet location. This does not cause any harm or disruption.
It is not possible to remove TDE once implemented. Even if there are no encrypted objects in the database, the TDE wallet has to be present in the wallet location. This does not cause any harm or disruption.
Ready to Implement TDE to Oracle EBS Release 12.2? Syntax Can Help.
Syntax has 40+ years of Oracle ERP experience and over 25 years of providing cloud and managed services for Oracle E-Business Suite applications. We provide automation-driven, best-of-breed private and public cloud offerings on Amazon Web Services (AWS), Microsoft Azure, and Oracle Cloud Infrastructure (OCI), as well as our own purpose-built enterprise data centers.
Contact Us
Contact us today to discover how we can improve the efficiency and effectiveness of your Oracle EBS environment.

